Cybercriminals compromised approximately 500,000 Microsoft 365 accounts in 2021
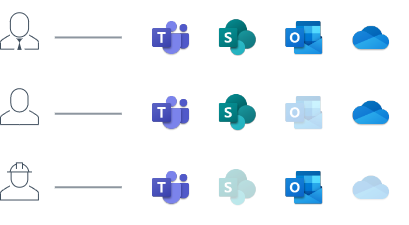
By exploiting the rise of remote work, BYOD policies, and a distributed workforce, cybercriminals are able to move laterally across Microsoft 365 applications.
Protect your Microsoft 365 applications from lateral attacks
Mitigate breach risks for your remote employees and contractors and reduce your exposure to lateral attacks by deploying continuous verification of user and device identity and trust.
Enable remote worker productivity
Empower employees with streamlined access to Microsoft 365 applications, increased security, and upgraded performance compared to traditional VPN technology.
Easily deploy and manage from the cloud
With flexible deployment, you can instantly provision company devices, BYOD endpoints, and contractor endpoints, or enable self-service for your workforce.
Quick to deploy, easy to manage Zero Trust Access for Microsoft 365 applications
Security starts with access. Barracuda’s Zero Trust Access model establishes unparalleled access control across users and devices — from remote to hybrid, and from company-owned to employee- and contractor-owned. It provides remote, conditional, and contextual access to resources and reduces over-privileged access risks. With Zero Trust Access, employees and partners can access Microsoft 365 applications without creating additional attack surfaces.
Secure third-party access to your business
Mitigate the risks associated with third-party access to your business with Zero Trust. Improve visibility into device and user activity and enable role-based access to applications and data. Deploy Zero Trust Access and secure access to Microsoft Outlook, Teams, OneDrive, SharePoint, and more for your outsourcers, partners, contractors, and post-M&A subsidiaries.
Protect your employees with dynamically-triggered multifactor authentication (MFA)
Turn your endpoint devices into an additional layer of defense against Microsoft account compromise. With Certificate-Based Authentication (CBA) and dynamically-triggered MFA, you can prevent advanced MFA bypass attacks and mitigate breach risk for your employees.
Simplify compliance reporting
Meet SOC Type 2 and other compliance requirements with no extra work. Zero Trust Access creates a clear system of record for your Microsoft 365 applications, delivering streamlined reports of system access across the organization. Manage, track, and verify the who, what, and when of privileged access in one product.