13 email threat types you need to know about
As email threats evolve and multiply, keeping track of them all — and staying protected against the many different types — becomes a complex challenge. Today, that requires more than just the traditional email gateway solution that used to be good enough.
Barracuda can help. Our research, based on real-time threat intelligence collected from more than 200,000 collection points around the globe, has resulted in the identification of 13 key types of email threats. Once you understand the nature and characteristics of these 13 threat types, you’ll be far better prepared to build the best protection for your business, data, and people.
91% of cyber attacks start with an email.
How to build effective protection against all 13 threat types
Traditional email gateways are still a critical part of your security infrastructure. But to protect against all 13 email threat types, you also need a newer type of solution: API-based inbox defense.
Unlike gateway solutions that use signature-matching and payload analysis to prevent threats from arriving to your inbox, API-based inbox defense solutions use historical communication data to spot anomalous emails that evade the gateway and land in users’ inboxes. Malicious emails are removed instantaneously.
| Threat Type | Barracuda (Email gateway + API-based inbox defense) | Email gateway-only solutions |
|---|---|---|
|
Spam
|
||
|
Malware
|
||
|
Data exfiltration
|
||
|
URL phishing
|
||
|
Lateral phishing
|
||
|
Spear phishing
|
||
|
Brand Impersonation
|
||
|
Domain Impersonation
|
||
|
Business email compromise
|
||
|
Scamming
|
||
|
Extortion*
|
||
|
Account takeover
|
||
|
Conversation hijacking
|
Think beyond the gateway to protect against all 13 threat types
To protect your organization from socially engineered attacks, you need an additional layer of defense beyond your gateway solution: API-based inbox defense.
Inbox defense relies on APIs to integrate directly with your users’ inboxes. This integration provides visibility into both historical and internal email communication for every individual in the organization. Communication data is used to train artificial intelligence (AI) to create a statistical model or an identity graph for each user that reflects their communication patterns.
Using historical data the model will define users’ regular email addresses, individuals they communicate with, the type of requests they make, and many other behaviors. When something abnormal happens that is outside of an individual’s identity graph, AI instantly flags it as malicious and removes it from the user’s inbox.
Types of requests
Names used
Location
Email Addresses
Document types
Sentiment Analysis
Contacts and relationships
Barracuda solutions offer a lot of value. They make it easy to protect our organization against advanced email threats like account takeover and to deal with incidents effectively. Barracuda helped tighten up our email security posture.

Barracuda Email Protection
Barracuda Email Protection multi-layered approach combines a secure email gateway, AI-powered fraud protection, advanced security awareness training and automated incident response. This results in comprehensive protection against all email threats from spam and malware to business email compromise and account takeover.
Discover threats hiding in your inbox right now with the free Barracuda Email Threat Scanner
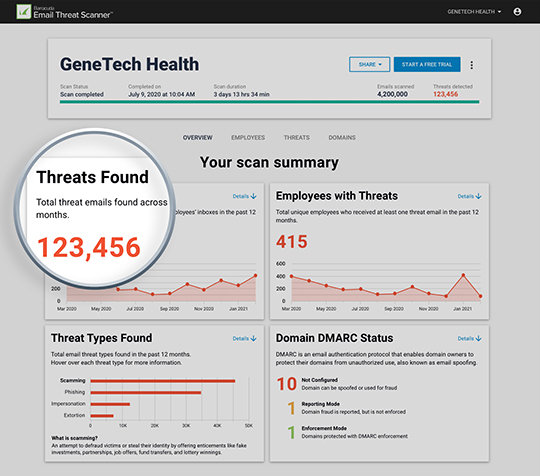
98% of organizations with Microsoft 365 harbor malicious emails inside their mailbox.* Discover email threats before your users do.
16,000+ organizations
have used the scanner to discover 12 million threats hiding in their mailboxes. Get your free scan now. It's fast, safe, and has no impact on your email performances. Barracuda Forensics and Incident Response can be used to remediate within minutes.
Protecting over 1 billion emails daily
Barracuda has been recognized as a leading provider of email security services for the past 17 years. Hundreds of thousands of organizations trust Barracuda for cybersecurity.



